Yes, your email can be hacked without a password. Hackers often employ various techniques that bypass the need for your email password altogether. These tactics range from phishing attacks that trick you into revealing personal information to exploiting vulnerabilities in the software you use daily. Hence, securing your email involves much more than just having a strong password.
A common approach involves phishing, where attackers lure you into providing personal details through deceptive emails or websites. It’s not just passwords they’re after; sometimes, they aim to gather enough information to answer security questions or use social engineering to gain access.
To combat these threats, it is vital to enable two-factor authentication (2FA) and stay vigilant. These measures provide an additional layer of security and make it significantly harder for hackers to compromise your email.
Hacking Email: More Than Just Passwords
Passwordless Attacks: How They Work
Hackers have many tricks up their sleeves, and not all of them rely on stealing your password. Here are some ways they can get into your email without it:
- Phishing scams: These emails look real and try to trick you into clicking bad links or giving out personal info.
- Keyloggers: This sneaky software records what you type, including passwords and other sensitive data.
- Data breaches: When companies get hacked, your email and other info might be exposed.
- Malware: This harmful software can infect your computer and steal your data, even without your password.
- Weak security questions: If your security questions are easy to guess, hackers can use them to reset your password.
Table: Common Passwordless Attack Methods
| Attack Method | How It Works | How to Protect Yourself |
|---|---|---|
| Phishing | Tricking you into clicking bad links or giving out personal info | Be wary of suspicious emails, don’t click on links from unknown senders, and never give out your password or personal info via email. |
| Keyloggers | Recording what you type, including passwords and other sensitive data | Use strong antivirus software and be careful about what you download. |
| Data breaches | Exposing your email and other info when companies get hacked | Change your passwords regularly and use different passwords for different accounts. |
| Malware | Infecting your computer and stealing your data | Use strong antivirus software and be careful about what you download. |
| Weak security questions | Resetting your password if your security questions are easy to guess | Choose strong security questions and answers that are hard to guess. |
Protecting Yourself: More Than a Strong Password
While a strong password is important, it’s not enough to fully protect your email. Here are some extra steps you can take:
- Two-factor authentication (2FA): This adds an extra layer of security by requiring a code from your phone or another device to log in.
- Update your software: Keep your operating system, web browser, and antivirus software up to date to patch security holes.
- Be careful on public Wi-Fi: Avoid logging into sensitive accounts like email on public Wi-Fi, as hackers can easily intercept your data.
- Check your email activity: Look for any unusual logins or sent emails that you don’t recognize.
- Use a password manager: This tool can help you create and store strong, unique passwords for all your accounts.
Remember, staying safe online is an ongoing process. By taking these precautions and staying informed about the latest threats, you can help keep your email and other accounts secure.
Key Takeaways
- Email can be hacked without a password.
- Phishing and social engineering are common hacking methods.
- Two-factor authentication enhances email security.
Understanding Email Security
Email security involves protecting your email accounts from unauthorized access and threats. Key components include recognizing common vulnerabilities, understanding types of attacks, and knowing the role of passwords.
Common Email Vulnerabilities
Email accounts can be vulnerable to several weaknesses. One major point of concern is weak or reused passwords. Hackers exploit these to gain unauthorized access to personal information. Security questions used for password recovery can also be a weak link if they are easily guessable or answerable from public data.
Additionally, malware and phishing attacks are significant threats. Malware like viruses or spyware can infiltrate devices and steal email login details. Poorly secured networks, particularly public Wi-Fi, can leave email data exposed to interception by malicious entities.
Types of Email Attacks
Several types of attacks can target email accounts. Phishing is the most common, where attackers send deceptive emails to trick users into revealing personal information. Spear phishing is a targeted version where attackers tailor their approach to individuals or organizations.
Malware attacks, including spyware and Trojans, aim to infect devices to steal credentials. Credential stuffing involves hackers using lists of breached passwords to attempt access on multiple accounts. Man-in-the-middle attacks on insecure networks can intercept email data, leading to identity theft and other security breaches.
Role of Passwords in Email Security
Passwords are the first line of defense in email security. A strong, unique password protects against brute-force attacks and unauthorized access. Two-factor authentication (2FA) adds an extra layer of security, requiring a second verification step like a code sent to a mobile device.
Email providers often offer tools and recommendations for creating and managing strong passwords. Avoiding common words or easily guessable phrases is crucial. Updating passwords regularly and avoiding reuse across different accounts further fortifies the security of your email data.
Preventing and Responding to Email Compromise
Effective strategies can help prevent email hacking and mitigate damage if it occurs. Key tactics include enhancing protection, monitoring activity, and taking decisive steps if compromised.
Strengthening Your Email Protection
Using a strong password and enabling two-factor authentication (2FA) add layers of security to your account. A strong password combines upper and lower-case letters, numbers, and symbols. Password managers can generate and store complex passwords efficiently.
Avoid using public Wi-Fi for accessing sensitive information without a VPN. An antivirus program can detect and remove malicious software that may compromise account security. Regularly updating your operating system and email application also helps protect against vulnerabilities.
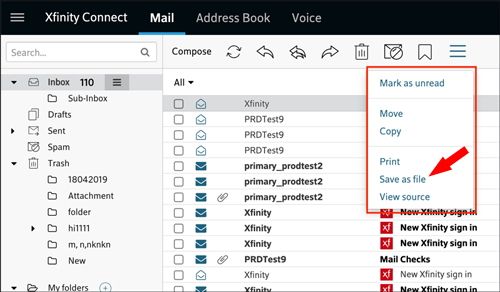
Monitoring and Detecting Suspicious Activity
Regularly checking account settings can help spot unauthorized changes. Verify that no malicious links are embedded in your email signatures and remove any unauthorized forwarding addresses.
Monitor your email account for unusual sign-ins, especially from unknown locations. Many email providers offer tools to review recent account activity. Stay vigilant for phishing attacks, and be cautious of unsolicited emails that ask for sensitive information.
What to Do If Your Email Is Compromised
Start by changing your email password immediately to something strong and unique. Enable two-factor authentication if it’s not already in place. Check and update your account settings to ensure no unauthorized changes have been made.
Inspect your contact list for any unfamiliar addresses that may have been added. Notify your contacts that your account was compromised to prevent them from falling victim to any spam emails sent by the hacker.
Lastly, run a comprehensive scan with your antivirus software to detect any threats on your device. If you’re unable to recover access, contact your email provider for assistance in the recovery process.
Frequently Asked Questions
Here are answers to some of the most common questions about email hacking, including how to protect your account and identify compromises.
How can I determine if my email account has been compromised?
Unusual login locations, unexpected password reset emails, or emails you did not send appearing in your sent folder can indicate a hacked account. It’s also important to monitor for other suspicious activity.
What steps should I take if my email has been hacked?
Immediately change your password and enable two-factor authentication. Notify your contacts of the breach and check your settings for unauthorized changes. Consider contacting your email provider for further assistance.
What risks are associated with someone obtaining my email address illicitly?
Once obtained, your email can be used for phishing scams, spam, or other malicious activities. Hackers may also attempt to access other accounts linked to your email.
What methods do hackers employ to access email accounts?
Hackers often use phishing, social engineering, or malware to gain access. They may also exploit vulnerabilities in email providers’ systems.
How can I protect my email account from unauthorized access?
Use strong, unique passwords and enable two-factor authentication. Regularly update your security settings and be cautious of suspicious emails or links.
Is it possible for my bank account to be compromised through a hacked email?
Yes, if your email is used for banking communications, a hacker could reset your banking passwords or gain sensitive information. Always secure your email to prevent such risks.